I’ve been monitoring the cybersecurity space for more than two decades, but cyber threats are evolving at a pace I’ve never seen before. As technology evolves and the use...
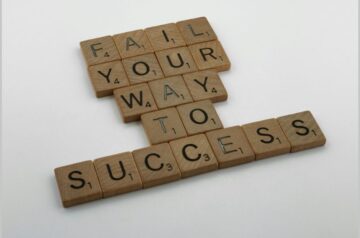
Failing Forward – How to turn Mistake into Great Success
In both business and life, failure is often seen as something to be avoided—a setback or mistake that signals a dead end. Yet, some of the most successful people...
How to Hire a Stellar Product Marketing Manager
On many occasions, I’ve been asked how to find and hire a great product marketing manager (PMM). For many, understanding the role can be tricky since the responsibilities often...
Marie Forleo – A Life Coach You Need To Know
Marie Forleo is a name synonymous with entrepreneurial success in digital business. Her journey from struggling to find her path to becoming a powerhouse entrepreneur is nothing short of...
Pat Flynn – From Architect to Successful Digital Entrepreneur
If you’re into passive income, you have to know Pat Flynn. He’s a successful online entrepreneur and host of the Smart Passive Income podcast. Pat is a prime example...
How Justin Welsh Built a Successful Solopreneur Business
“Don’t you know who Justin Welsh is?” a former colleague asked me a while ago. As I immersed myself in the world of content creation I came to know...
How to Effectively Expand Into a New Customer Segment
You can grow so much by focusing on a single customer segment. Expanding into new market segments is essential for business growth but it’s a strategic move that requires...
Online Privacy – A Quick Guide To Data Protection Regulations
We live in an era where digital footprints are as significant as a physical presence. Understanding how to protect personal and business data and knowing your rights is more...
How to Manage the Threats to Your Online Privacy
Have you ever noticed ads for items you’ve just searched for popping up on different websites you visit? This isn’t a coincidence; it’s a result of online tracking and...