How the Browser Redraws Security Categories
The signal In recent months, multiple independent incidents have shown the browser becoming not just a gateway for users, but a primary locus of risk, especially concerning authenticated sessions and…
Most popular
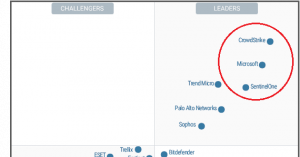
Signals Cybersecurity Market Index (SCMI)
Why another industry index Cybersecurity market indexes alre…
Win at Positioning: How Cybersecurity Leaders Differentiate
In the ever-evolving landscape of cybersecurity, differentia…
Positioning strategy: How to drive growth
The product positioning strategy is the cornerstone of any e…
Latest articles
Identity Becomes Runtime Critical Infrastructure
The Signal Over the past few weeks, several independent move…
Signals Cybersecurity Market Index (SCMI)
Why another industry index Cybersecurity market indexes alre…
CES 2026: Where Security Is Moving
CES is not the typical cybersecurity event. But when looking…
2026 Outlook: From Prevention to Personal Digital Resilience
For a long time, cybersecurity was synonymous with preventio…
Cybersecurity Market 2025: Which Companies Capitalized Best And Why
1. Industry Structural Changes 2025 mattered for cybersecuri…
2025 Cybersecurity Industry Review
From a cybersecurity perspective, 2025 didn’t follow a singl…