Cybersecurity behaves like software most of the time. But during systemic stress it can detach and trade on its own narrative. The Signals Cybersecurity Market Index (SCMI) chart from the past weeks illustrates that shift clearly.
Through February 27, SCMI largely tracked the broader technology trend. Directionally it moved in line with Nasdaq 100 (QQQ) and S&P 500 (SPX). The sector showed more volatility and deeper drawdowns, but the regime was the same: cybersecurity trading as high-beta software.
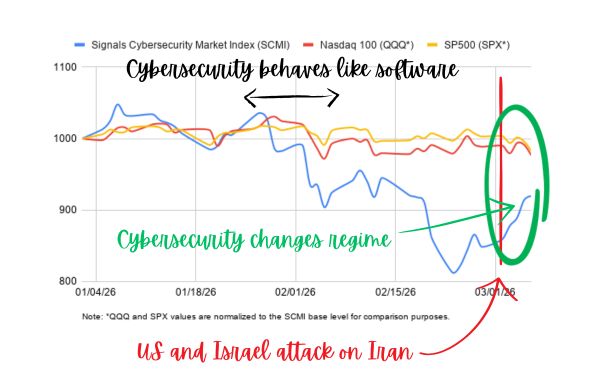
Fig. Cybersecurity detaches from big tech software
Around February 28, the pattern begins to change. The sector stops behaving purely as a tech multiple trade. Cyber does not suddenly become “defense,” but the narrative shifts toward operational resilience.
SCMI declined from 1047.8 on January 7 to 812.3 on February 23, a 22.5% drop. By March 3 the index had recovered to 878.2, and the rebound continued through the following sessions, reaching 919.7 by March 6.
Over the same period the broader market weakened. SPX declined from 1003.4 on March 2 to 982.7 by March 6, while QQQ fell from 989.8 to 976.5. This divergence is small in absolute terms, but important conceptually. For the first time in weeks, cybersecurity was recovering while the broader technology trend softened, suggesting the sector was beginning to trade on its own narrative.
The behavior inside the index is also relevant. Leadership rotated across names associated with resilience and operational control. Cloudflare (+5.1%) and CrowdStrike (+3.4%) led the rebound on March 2. On March 3 the move broadened to Rapid7 (+5.2%), Akamai (+4.6%), Zscaler (+4.1%), and Palo Alto Networks (+4.0%). By March 5, Okta (+10.9%) and Rapid7 again appeared among the strongest performers.
That pattern does not support the simplistic interpretation that “war makes cyber stocks go up.” What it suggests instead is that systemic stress changes how the market evaluates the sector.
The First Repricing: Platformization and AI
To understand the February 28 inflection point, it helps to look at what was already happening before.
Cybersecurity valuations had already been under pressure from two structural forces.
The first is platformization. Security budgets are consolidating around broader control planes. Vendors that own enforcement layers or operational workflows gain leverage. Vendors that primarily provide visibility or posture mapping face increasing pressure to justify why they remain standalone purchases.
The second force is AI-native tooling beginning to compress differentiation across parts of the security workflow.
The release of Anthropic’s Claude Code Security triggered a wave of commentary about whether AI systems could replace traditional security vendors. That framing is simplistic, but the underlying investor question is legitimate. If AI can industrialize vulnerability discovery, code review, and remediation suggestions, parts of the security stack that once commanded premium pricing become harder to defend.
Anthropic positions the tool as a way to scale vulnerability discovery and defensive code review directly inside development workflows. Reports that the system identified large numbers of vulnerabilities in widely used software projects amplified the perception that AI could accelerate portions of the security workflow.
The important point is not whether Claude replaces vendors. It does not. The point is that AI reduces differentiation in narrow slices of security work, particularly where workflows are repetitive or data-heavy.
Platformization and AI reinforce each other. Platforms concentrate distribution and budget authority, while AI compresses differentiation across certain functions. Together they push leverage toward vendors that control enforcement, identity, network flow, and response workflows.
Up to February 27, that repricing still lived inside the broader tech market regime. Cybersecurity was underperforming, but it was underperforming as software.
When the Narrative Changes: War and Resilience
The geopolitical escalation changes the narrative context.
On February 28, the United States and Israel launched strikes on Iranian targets, introducing a new layer of geopolitical uncertainty. Government assessments and vendor reporting quickly highlighted the risk of retaliatory cyber activity, including DDoS campaigns and disruption attempts associated with Iranian-aligned actors.
That threat pattern is predictable. Early cyber activity in geopolitical escalation is usually disruptive rather than catastrophic. It aims to create friction, visibility, and economic noise rather than immediate systemic failure.
But the perception of stress is what matters for markets. When the risk environment deteriorates, buyer psychology changes quickly. In stable periods, security discussions revolve around efficiency and coverage. Organizations debate feature depth, integrations, dashboards, and incremental improvements to visibility.
Under stress, those debates compress. Boards and security teams begin asking simpler questions: Can we stay online? Can we contain incidents quickly? Can we recover cleanly? Resilience and operational control become the dominant concerns.
That shift does not necessarily create new demand. But it changes which layers of the security stack appear essential. Infrastructure and enforcement layers gain relative importance, while pure visibility or governance layers face greater scrutiny.
In that sense, the geopolitical escalation did not reverse the structural repricing already underway in cybersecurity. It reinforced the same hierarchy shift, but through a different lens.
Cybersecurity Is a Category of Its Own
This dynamic reflects a broader characteristic of the sector.
Cybersecurity occupies an unusual position in capital markets because it can switch regimes faster than most technology industries. Most of the time it trades like growth software. Valuations move with discount rates, macro sentiment, and broader technology multiples. Investors debate product differentiation, pricing power, and expansion opportunities.
But during systemic stress events, the narrative shifts.
Cybersecurity begins to look less like software and more like operational infrastructure. Investors focus less on feature expansion and more on reliability, control, and which vendors remain indispensable when systems are under pressure.
The last few trading sessions illustrate that transition. Between March 2 and March 6, SCMI rose from 859.8 to 919.7, while the broader market weakened. Over the same interval SPX declined from 1003.4 to 982.7 and QQQ from 989.8 to 976.5.
Short windows like this are not enough to define a new regime. But they illustrate an important point: when the narrative shifts toward operational resilience, cybersecurity can temporarily detach from the broader software trade.
That is why simplistic explanations rarely capture what is happening. Cyber stocks did not fall because Claude released a tool. They did not rebound because war increases cyber risk.
The underlying mechanism is leverage reallocation. Platformization pushes leverage toward control planes. AI compresses differentiation in certain workflows. Geopolitical stress reinforces the importance of operational resilience.
Cybersecurity is software, until it isn’t.
